CodeTwo signatures are not added to emails in Microsoft 365 - Troubleshooting
Problem:
Signatures created with CodeTwo Email Signatures 365 are not added to emails.
Solution:
There might be several reasons why your messages do not receive signatures. Some reasons will be different for every signature mode in which CodeTwo Email Signatures 365 works (cloud/server-side, Outlook/client-side, or combo), while other are common to all the modes. The most common issues and recommended solutions are described below.
General issues:
- A Microsoft 365 tenant is not registered in CodeTwo services
- Incorrect signature mode selected
- Free trial period or subscription expired
- Number of licenses exceeded
- Scope of licensed users changed
- Initial synchronization/configuration of the program is not complete
- OAuth 2.0 access tokens expired
- Users recently added to a distribution group do not get signatures
- Unsupported message type
- Missing signature template formats (HTML, Plain Text)
- A message does not meet conditions/exceptions of a signature rule
- A group specified in signature conditions no longer exists in your Microsoft 365 tenant
Cloud (server-side) mode specific issues:
- Missing connectors configuration
- A message sender is not included in the outbound connector
- Incorrect rule setup (conditions & logic)
Outlook (client-side) mode specific issues:
- Unsupported Outlook version
- The CodeTwo Web Add-in for Outlook is still being deployed
- CodeTwo Web Add-in for Outlook is not deployed correctly
- Exceeded character limit for your HTML signature
- Missing or inactive Outlook (client-side) rules in the signature management app
Combo mode specific issues:
Issues specific to all modes
A Microsoft 365 tenant is not registered to CodeTwo services
Tenant registration is required for CodeTwo Email Signatures 365 to operate in any of the modes. If signatures are not added to messages sent by any user, make sure that your tenant has not been deregistered or that it has not been blocked for any reason.
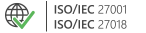
To check the status of your tenant, open CodeTwo Admin Panel and see if your tenant is visible on the Tenants page (Fig. 1.). If not, you need to register it. To do so, click ADD TENANT button and follow the instructions, as described here.
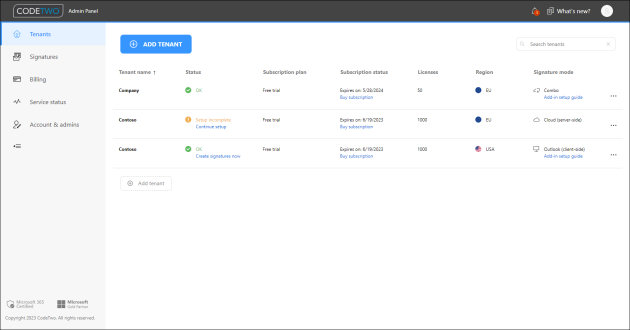
Fig. 1. The list of Microsoft 365 tenants registered to CodeTwo.
Incorrect signature mode selected
There are three signature modes available: cloud (server-side), Outlook (client-side), and combo. When CodeTwo Email Signatures 365 operates in cloud mode, Outlook signatures will not work (and vice versa). However, both types of signatures work in combo mode. If your signatures are not added to emails as expected, make sure you have selected the correct signature mode. To learn more about signature modes read this article.
To see which mode is currently selected, go to the Tenants page in CodeTwo Admin Panel and have a look at the information in the Signature mode column for your tenant (Fig. 2.).
Fig. 2. The information about the selected signature mode.
If you want to change the signature mode, see this article for step-by-step instructions.
Free trial period or subscription expired
If your free trial version or your paid subscription plan expires (as shown in Fig. 3.), no email signatures will be added to your emails. You need to buy/renew your subscription. To learn how to check the status of your subscription and how to buy/renew a subscription, visit the Licensing section of the user's manual.
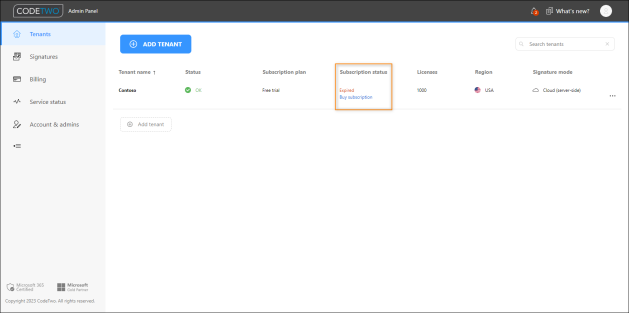
Fig. 3. The message shown for the tenant whose trial period expired.
Number of licenses exceeded
If some of your users get signatures in their emails while others don’t (especially new users), you might have exceeded the number of available licenses:
- In the case of cloud (server-side) signatures, this situation may occur when you have configured the program's connectors incorrectly, and the scope of senders (users who should get cloud signatures) is too wide – it covers more users than the number of licenses you purchased. Note that every sender whose email travels through CodeTwo uses one license from your license pool, no matter if this user is defined in any signature rule.
- In the case of Outlook (client-side) signatures, licenses are consumed in a different way, depending on the Outlook add-in’s deployment and the configuration of Outlook signatures for a given user. If the number of licenses is exceeded, some of your users might not get any signatures, and CodeTwo's signatures add-in for Outlook will show them a specific error message.
Learn more about how licenses are counted and assigned
To solve the problem of excessive license consumption, regardless of which signature type(s) you use, you can limit the scope of licensed users, as described in this article.
If you only want to limit the number of users that get a specific type of signature, proceed as described below:
- Cloud (server-side) mode: reconfigure the connectors and specify the scope of senders who will receive signatures. To do so, open the Admin Panel's Tenants page, click your tenant, select Exchange Online connectors in the menu on the left, and click Configure connectors automatically. Then, follow the steps described in the user's manual. If necessary, you can also reconfigure the connectors manually.
- Outlook (client-side) mode: deploy the Outlook add-in for a selected group of users only. More information about the deployment can be found here. This allows you to limit license consumption to only those users who are intended to receive Outlook (client-side) signatures in their emails.
- Combo mode: use the method for resolving the issue in cloud (server-side) mode as well as the method for Outlook (client-side) mode to reduce the number of consumed licenses.
You can check the number of used licenses and which accounts are using them by opening the Licensing page for your Microsoft 365 tenant in CodeTwo Admin Panel, as shown in Fig. 4. See this article for details.
Once you perform the necessary steps, you need to reset the license count on the Licenses page in CodeTwo Admin Panel. To do so, select your tenant, click Licenses in the left menu, and click Reset signature license count or Reset autoresponder license count, depending on which type of licenses you want to reset (Fig. 4.).
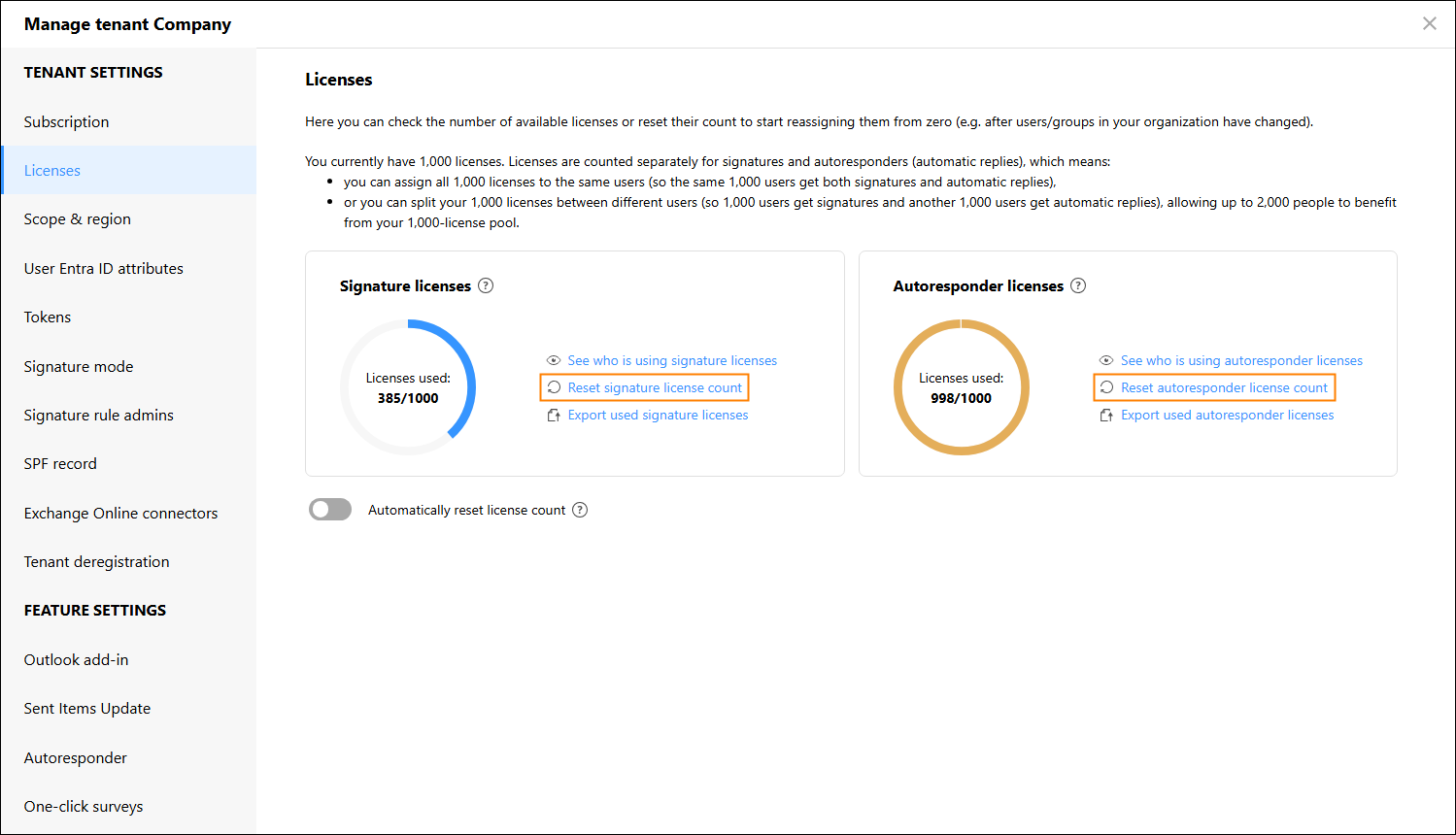
Fig. 4. Resetting license count on the Licenses page.
If you narrowed down the scope of users who can get email signatures and reset the license count, but the problem persists, it is possible that your subscription requires additional licenses. Please contact our Support Team to consult this.
Scope of licensed users changed
Only the users specified in the Scope & region section in tenant settings (Fig. 5.) can synchronize to CodeTwo to get signatures and consume licenses. If you've changed/limited the scope, some of your users might stop getting signatures. Learn more
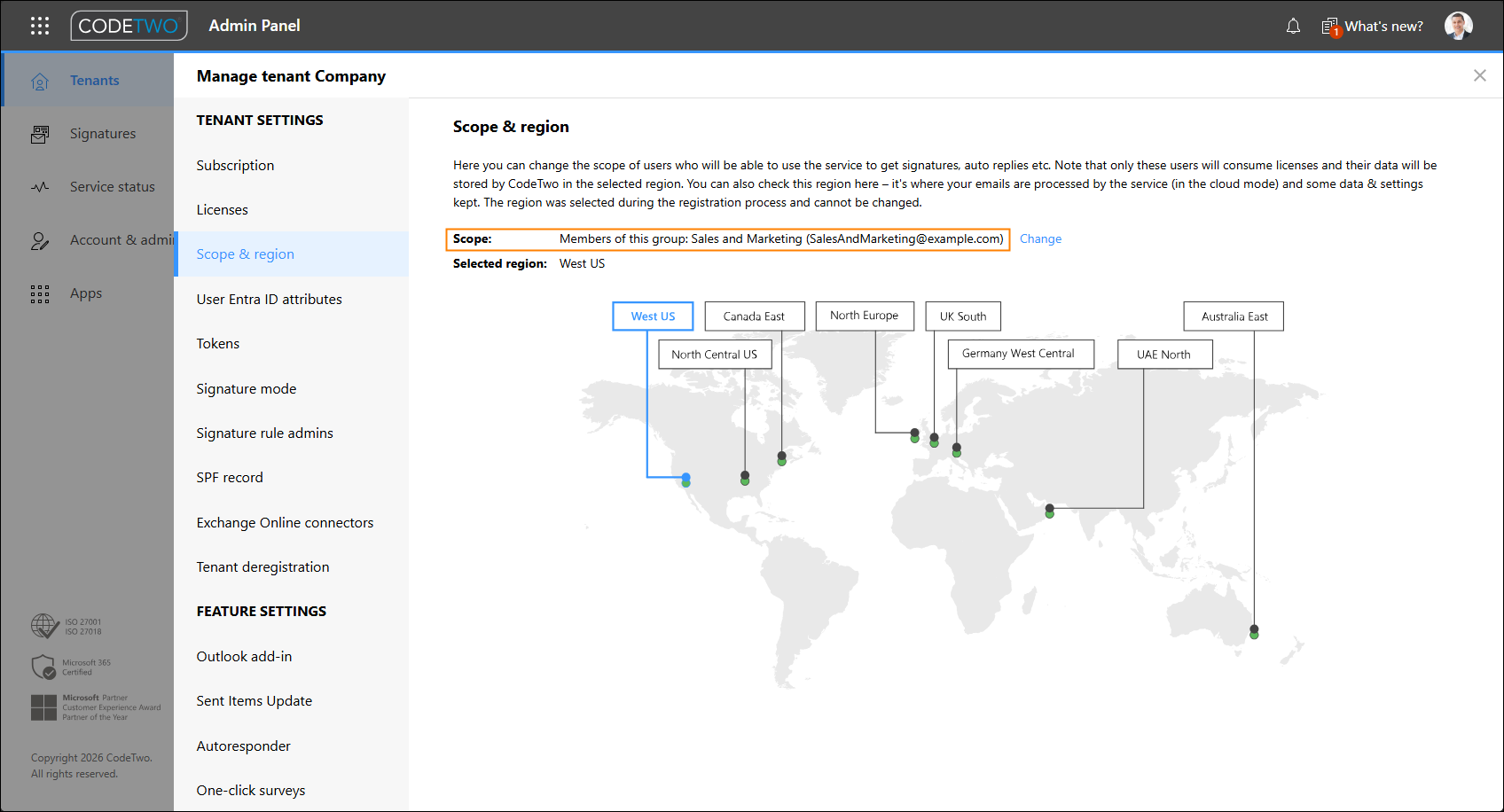
Fig. 5. The scope of users who can benefit from the CodeTwo service (in this example, the scope is limited to a group).
If you've removed the group of users specified in the Scope & region section in tenant settings from your Microsoft 365 (Entra ID), signatures will no longer be updated. Learn more
Initial synchronization / configuration of the program is not complete
If you configure the program for the first time for your tenant, remember that some of your emails might not get signatures until the initial synchronization is over. The application needs to save the required Microsoft Entra ID attributes of your users in an internal cache called Entra ID CodeTwo cache (read more in this article). The service holds a local copy of your Entra ID properties to instantly add Entra ID-based placeholders to email signatures, without the need to constantly query your Entra ID data. The first syncing process might take a while. You can check the status of initial synchronization in CodeTwo Admin Panel: enter the management pages of your tenant by clicking the tenant (on the Tenants page), then select User Entra ID attributes from the left menu. If you can see the date of the Last cache update (as shown in Fig. 6.), this means that the syncing is finished.
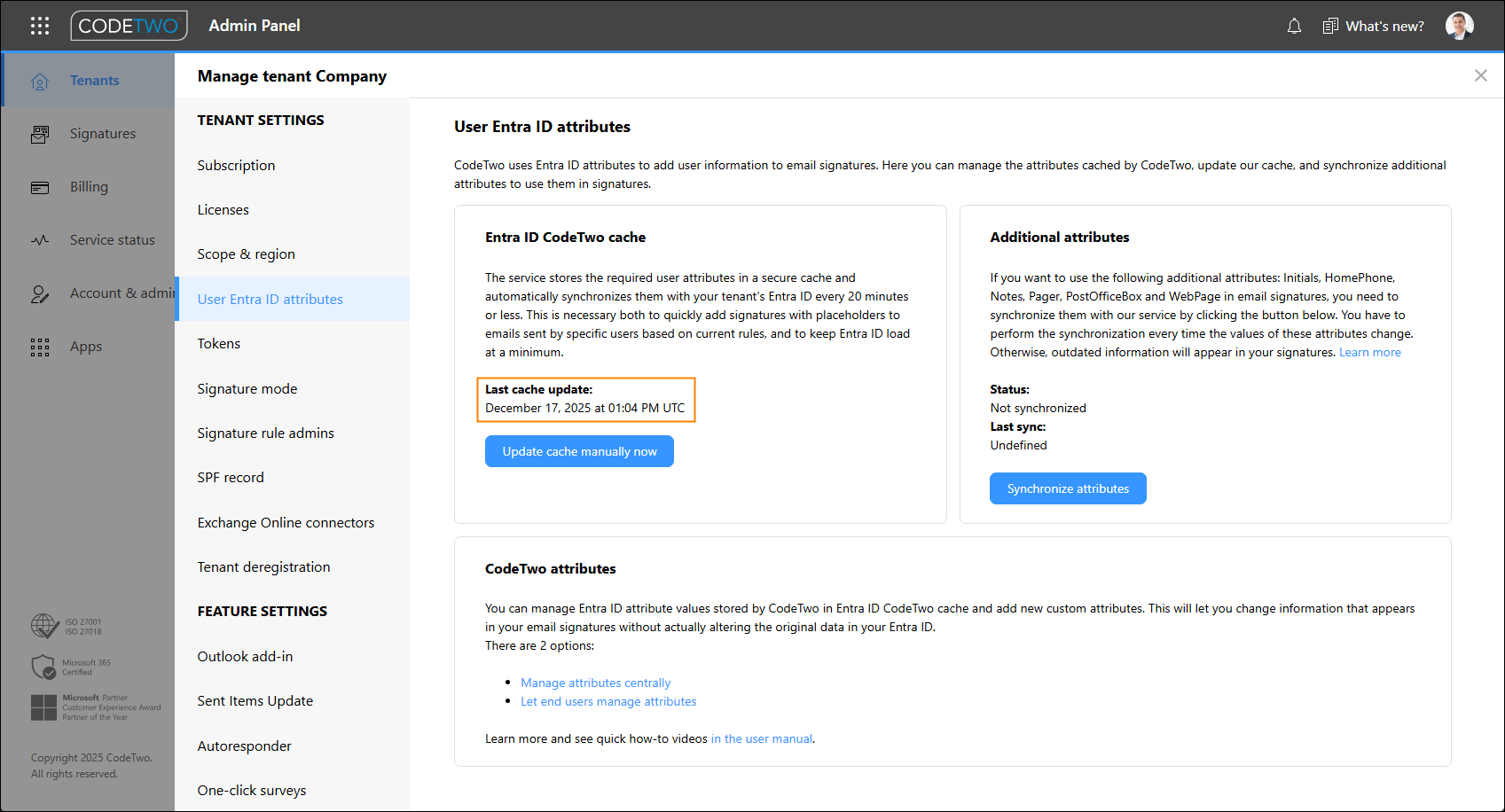
Fig. 6. The status of Entra ID CodeTwo cache synchronization.
If the Entra ID attribute synchronization is still in progress, you will see no date or the following information: Synchronizing now... (see Fig. 7.). Until the process is completed, your users might not get email signatures.
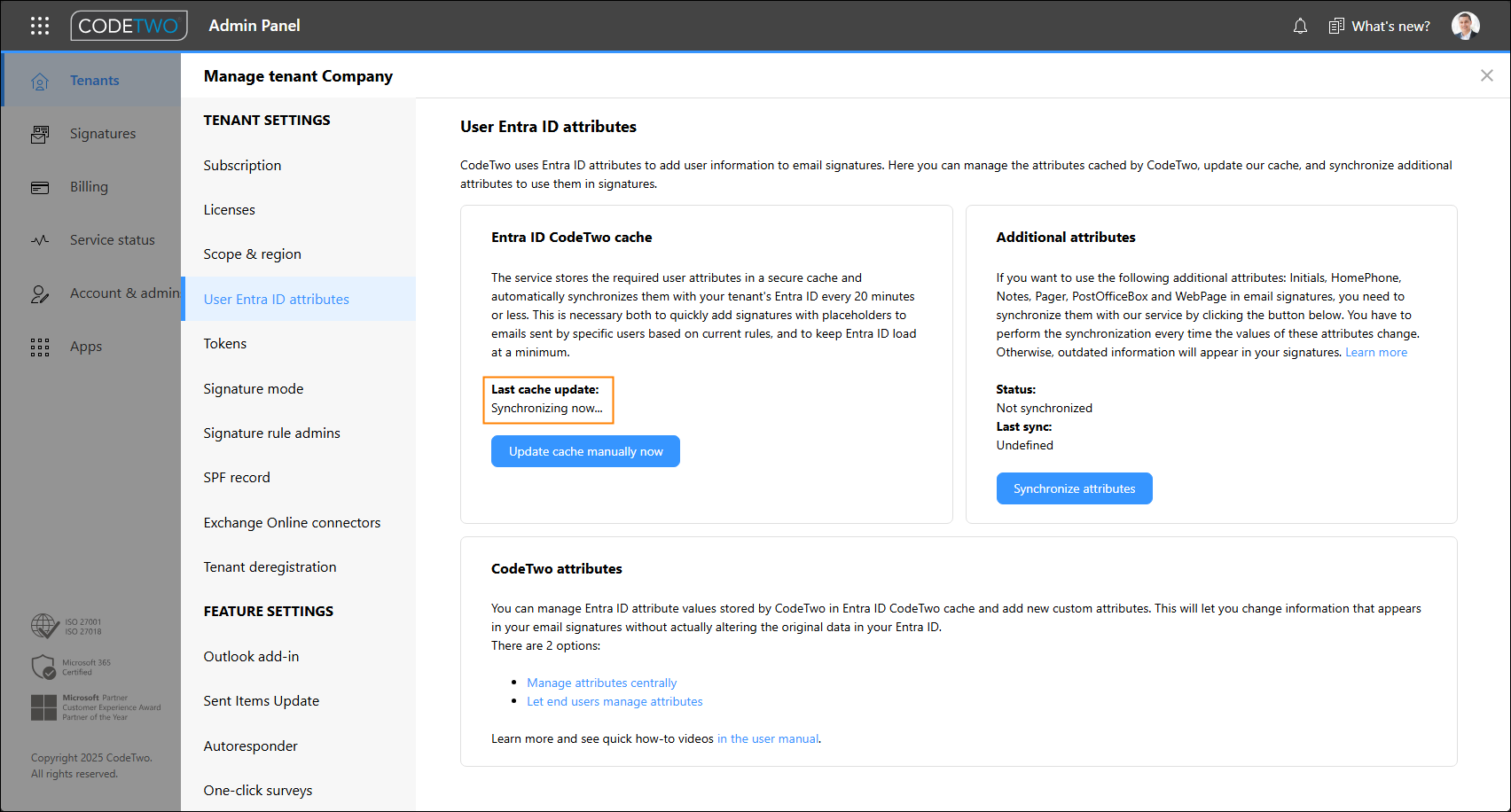
Fig. 7. Initial synchronization in progress.
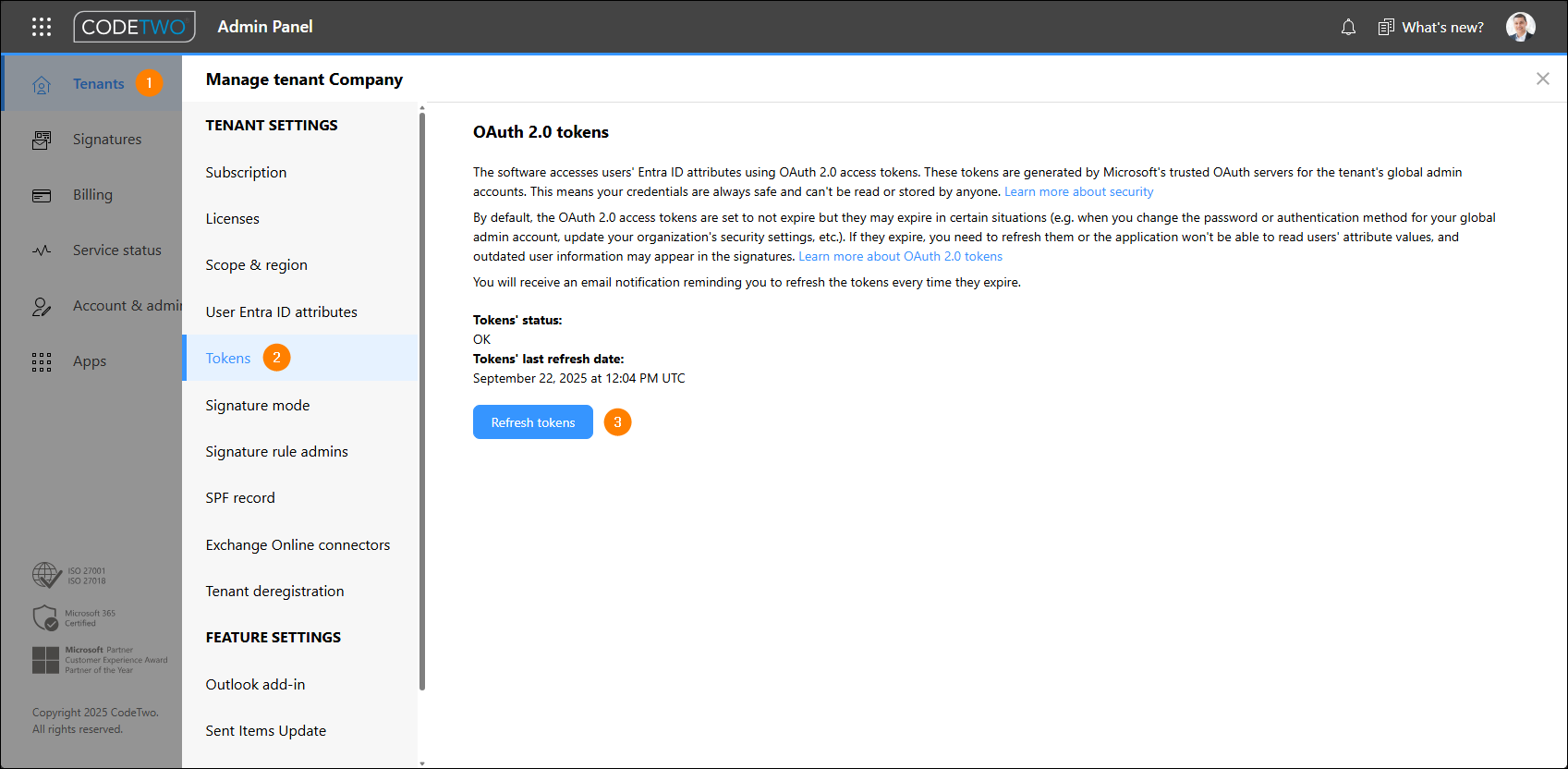
OAuth 2.0 access tokens expired
OAuth 2.0 access tokens are used to read organization's Entra ID data. These tokens are set to not expire under normal circumstances but may do so in certain circumstances (see the user's manual for details) and need to be refreshed. If the access tokens expire and you modify your Entra ID data without refreshing them, our software is not able to recognize your changes. For example, if your tokens are not valid and you add a new user to an Entra ID group that is also defined (in the Senders step of your signature rule in the signature management app) as the group of senders who trigger your signature rule, then this change will not be applied and this user will not get any signature. To fix this, refresh the tokens (Fig. 8.), as explained in our user's manual.
Users recently added to a distribution group do not get signatures
If you recently added new users to a distribution group/list that contains people in your organization whose emails receive signatures, these new users might not be able to get their signatures immediately. This may happen in the case of cloud (server-side), Outlook (client-side), and combo modes.
Warning
Remember that each time you modify a distribution group (e.g. add new users), it can take from a few minutes to a few hours for the changes to propagate in your Microsoft 365. Email signatures created in the program might not be added to messages sent from new users during that time.
Unsupported message type
Certain email types are currently not supported by the program and will not receive signatures. See the user's manual to learn about the unsupported message types.
Missing signature template formats (HTML, Plain Text)
By default, the built-in signature editor opens on the HTML tab (Fig. 9.) that allows you to design a signature for most email clients. However, messages can also be sent in Plain Text (e.g. emails from mobile devices). Always prepare your signature templates in all available formats to make sure that signatures are always added. Learn more
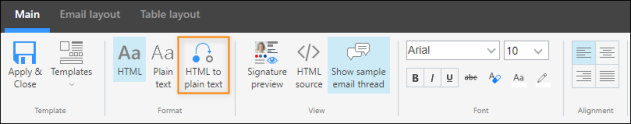
Fig. 9. Convert tool in the signature editor.
Info
If you prefer to add HTML signatures also to emails sent in Plain Text, you can force the program to convert Plain Text emails to HTML. Learn more.
A message does not meet the conditions/exceptions of a signature rule
When you create a signature rule, you define various conditions that need to be fulfilled in the Senders, Recipients and Keywords steps. By default, all of these conditions have to be fulfilled to trigger a rule and add a corresponding signature. In other words, if at least one condition is not fulfilled, an email will not receive a signature.
If your signatures are not added to your email, please review the Senders, Recipients and Keywords conditions to make sure that the message fulfills all of them.
As for the exceptions defined in the program, remember that a signature rule is suppressed for each exception individually. Learn more about conditions and exceptions.
Info
Outlook (client-side) signatures only use the Senders rules and conditions.
A group specified in CodeTwo no longer exists in your Microsoft 365 tenant
When setting up conditions for signature rules in CodeTwo's Signatures app, you can select groups or distribution lists in your tenant to specify which users will get signatures. If you delete these groups later in your Microsoft 365 tenant, these rules will no longer work. Be sure to double-check your rule configuration against your tenant. If any groups are missing, create new ones or make changes to your CodeTwo rules.
Learn more about signature rule configuration in CodeTwo
Cloud (server-side) mode specific issues
Missing connectors configuration
Inbound and outbound connectors must be configured if you want to use CodeTwo Email Signatures 365 in cloud or combo mode.
To check the status of connectors, go to the Tenants page of CodeTwo Admin Panel. If you can see the Connectors configuration required message in the Status column for your tenant, you need to configure the connectors. You can do it manually or via the connectors configuration wizard. To launch the wizard, click the tenant, select Exchange Online connectors from the left menu and click Configure connectors automatically (Fig. 10.). Then follow the steps described in the user's manual.
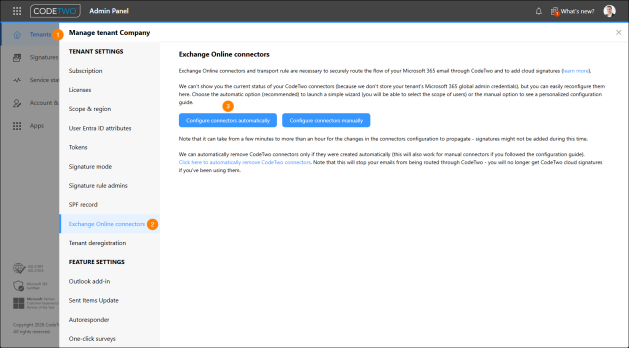
Fig. 10. The connectors configuration page.
A message sender is not included in the program's outbound connector
This problem occurs when there is a mismatch between the senders you defined for the program's outbound connector and the senders you indicated in a signature rule.
During the configuration of Exchange Online connectors for your tenant, you specify users (senders) whose emails should travel through the CodeTwo cloud service. This setup step (Fig. 11.) concerns the program's outbound connector and the associated transport rule. In the example below, only the outgoing (external) emails from specified senders (e.g. the Executives in the figure below) will be routed through the CodeTwo service.
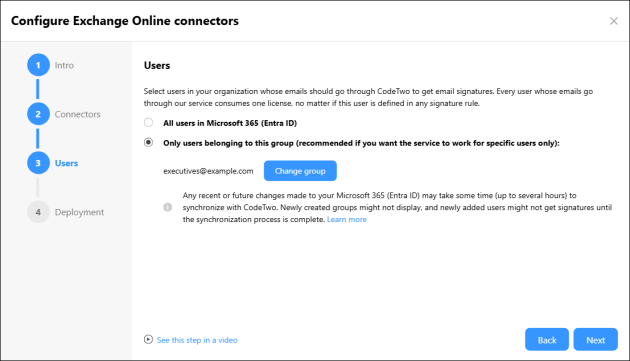
Fig. 11. The connectors configuration wizard in CodeTwo Admin Panel.
When the users you specified send messages, the CodeTwo cloud service checks them against your signature rules and adds signatures only to emails that match the conditions defined in these rules. If you create a signature rule with the Senders condition (Fig. 12.) defined for users who are not included in the outbound connector, their emails will not receive any signatures.
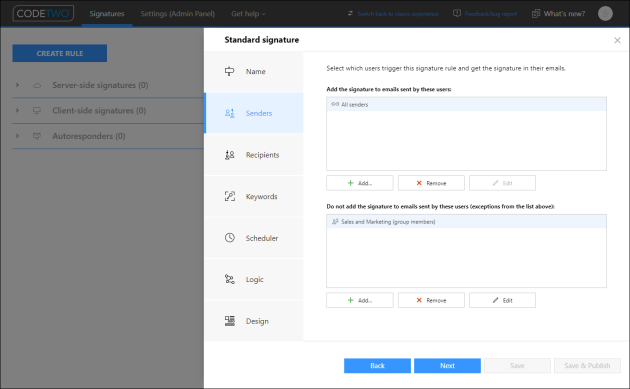
Fig. 12. Configuration of Senders in the signature management app.
Such mismatch is shown in the figures above: the rule adds signatures only to all users except from the members of the Sales and Marketing group (as shown in Fig. 12.). However, only emails of users from the Executives group (see Fig. 11.) are forwarded to the CodeTwo service to get signatures.
To solve this problem, you need to reconfigure the connectors to extend the scope of senders. You can do it manually or via the connectors configuration wizard. To launch the wizard, sign in to CodeTwo Admin Panel, go to the Tenants page, click your tenant, select Exchange Online connectors from the left menu, and click the Configure connectors automatically button. Then follow the steps described in the user's manual.
If you would like to learn more about manually adding and removing groups and users, read this article.
If email signatures are not added to your shared mailboxes only, make sure that you properly included them in the scope of senders. Learn more
Incorrect rule setup (conditions & logic)
If a single user doesn’t get a signature, it might mean that one or more cloud (server-side) signature rules are configured incorrectly. To check this, use the signature rules tester.
Troubleshooting rules set up for aliases
The signature rules tester currently only lets you test rules configured for primary email addresses. If you have cloud rules set up for alias addresses and your users don't get the correct signature, do the following:
- make sure that the rules configured for alias addresses are at the top of your cloud (server-side) signatures list, above the rules configured for primary addresses (see Fig. 13.),
OR - add alias addresses as exceptions to the rules configured for your primary email addresses.
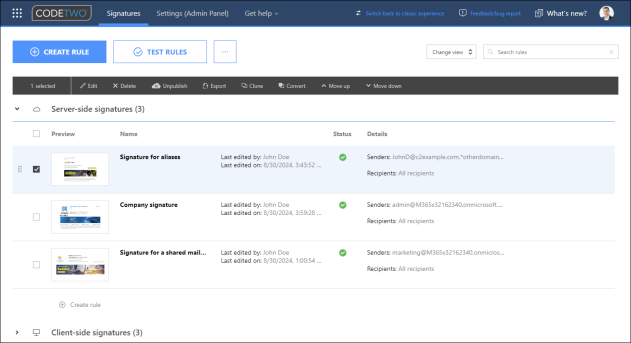
Fig. 13. Placing the rule for alias addresses at the top of the cloud (server-side) signatures list.
Learn in detail how to set up your cloud rule conditions and logic in a correct way
Outlook (client-side) mode specific issues
Unsupported Outlook version
The CodeTwo Signatures Web Add-in for Outlook & OWA will work correctly only with supported versions of Outlook.
The CodeTwo Web Add-in for Outlook is still being deployed
The deployment can take from 6 up to 72 hours to complete. Your users will begin receiving CodeTwo signatures once the Web Add-in appears and starts functioning in their Outlook apps.
CodeTwo Web Add-in for Outlook is not deployed correctly
When you deploy the Web Add-in via the Microsoft 365 admin center, you need to define users who will get the add-in and, consequently, will be able to use Outlook (client-side) signatures. Make sure you’ve made the add-in available to the right people from your organization. Even though you’ve defined certain users as senders in a given rule, they might not get signatures simply because they were not included in the deployment.
Also, the central deployment via the Microsoft 365 admin center is recommended to ensure the optimum experience. Even though your users can install the add-in individually, they won’t be able to make use of the automatic signature insertion feature. Learn more
Exceeded character limit for your HTML signature
Outlook supports a maximum of 120,000 characters for an HTML email signature. If your signature exceeds this limit, our Web Add-in won't be able to add it to your email.
Missing or inactive Outlook (client-side) rules in the signature management app
If you want Outlook (client-side) email signatures to work correctly, you need to set up Outlook (client-side) signature rules in the signature management app before the users begin using either of the two CodeTwo signatures add-ins for Outlook. If these rules are not configured, signatures will not be added.
When you prepare signature rules, make sure that they are published. You need to click the Save & Publish button (Fig. 14.) to apply changes to your organization. Clicking the Save button will save your rule without publishing.
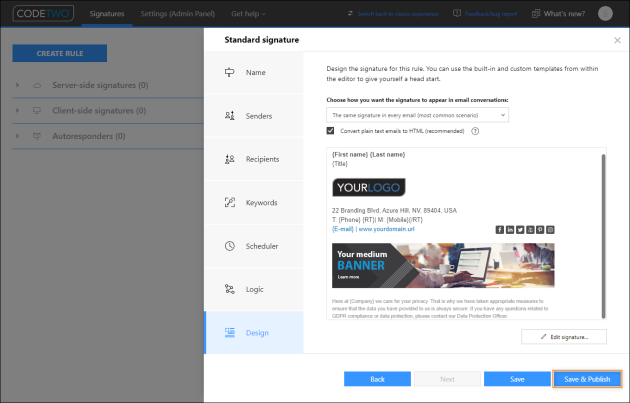
Fig. 14. Saving changes and publishing the signature rule in the signature management app.
Make sure to define users in the Senders step that you want to have access to the Outlook (client-side) signature applied by the given rule. You can include individual users or distribution groups, in which case all members of the group will be affected by the rule. Remember that if you recently added users to a group, this change might take some time to propagate.
Also keep in mind that cloud (server-side) and Outlook (client-side) signature rules work independently from one another. Even if a user would have been affected by a cloud rule existing in an earlier configuration, new rules need to be prepared when configuring CodeTwo Email Signatures 365 to operate in Outlook mode. It is also important to be aware of this when using combo mode.
Find out how to convert signature rules automatically from cloud to Outlook and vice versa
Combo mode specific issues
Identifying problems with cloud (server-side) and Outlook (client-side) signatures
Combo mode combines the features of cloud and Outlook signature modes, which means that to troubleshoot a problem with adding signatures, you should first establish whether it is a cloud or an Outlook signature that is causing an issue. Remember that any user or shared mailbox might be subject to Outlook and cloud rules.
| Related products: | CodeTwo Email Signatures for Office 365 |
| Categories: | Troubleshooting |
| Last modified: | January 30, 2026 |
| Created: | February 22, 2017 |
| ID: | 618 |