
YubiKey is one of the most popular security keys on the market. A security key is a small device that lets you authenticate yourself when you sign in to a service (e.g. Google, Facebook, email clients, etc.) using a multifactor authentication (MFA, 2FA). It can support multiple authentication standards, also in the Microsoft 365 ecosystem, and is far safer than, for example, the SMS code verification.
Security key types
The YubiKey devices available on the market differ in terms of the communication interface:
- USB keys – these are offered in USB-A or USB-C standard. To confirm your identity, you usually insert such key just like a thumb drive, enter a PIN you specified during setup and touch the device. You can also buy devices with a biometric reader, which you can use to register one or more fingerprints to use instead of a PIN.
- NFC keys – near-field communication keys are designed primarily with mobile devices in mind. The NFC feature often comes with USB keys.
- BLE keys – you can also buy Bluetooth Low Energy devices, but they are less safe because of the design of the Bluetooth standard.
What are the benefits of using YubiKey devices?
Security keys (U2F) are currently regarded as the safest method to secure an account, offering the following key benefits:
- Passwordless sign-in – passwords are not stored on a device, so a hacker cannot intercept them, even if your device is lost or stolen.
- Passwordless authentication – protects you against phishing.
- Plug-and-play solution – a key requires neither drivers nor additional software installation.
- Impervious to advanced attack methods like SIM-swap or MFA Fatigue / Push Bombing, that can be used to remotely hijack SMS or authentication app users’ accounts.
What are the YubiKey-supported authentication standards?
The latest 5th generation of YubiKey devices supports a number of authentication standards:
- WebAuthn – the standard lets you authenticate with a given service using a compatible browser coupled with the so-called external authenticator (e.g. your security key). For example, if you have registered a key in Entra ID / Microsoft365, the authentication of your account is initiated by your key through a supported browser (e.g. Chrome or Edge) and continued in the target service later on. WebAuthn is one of the key components of the FIDO2 project and provides the protection against phishing – mainly because it supports passwordless authentication.
- FIDO U2F – it’s a standard co-developed by Yubico and Google to improve the safety of the traditional login-password authentication with a YubiKey device, drawing on its cryptographic features (public and private keys are generated on each sign-in).
- FIDO2 – it’s an extension of the FIDO U2F standard which, most importantly, adds support for the passwordless sign-in. As you don’t have to provide login and password, a key can be associated with multiple accounts.
- Smart card – it’s a physical authentication device usually used in access control systems. If equipped with the NFC feature, a YubiKey device can play such a role, provided a device with controlled access is equipped with a physical smart card reader. If not, you can buy an external USB reader.
- Yubico OTP – a YubiKey device is also capable of generating one-time passwords (OTP) for those services that support this feature. The method resembles the verification with an SMS code.
- OATH-TOTP – TOTP stands for ‘time-based one-time password’ that’s generated in the Yubico Authenticator and expires after 30 seconds. Once the time has elapsed, a new password is generated.
- OATH-HOTP – works similar to OATH-TOTP but there is no time limit to use a password.
- OpenPGP – it’s an open standard used mainly to encrypt emails.
- Secure Static Passwords – a YubiKey device can store a static user-defined password. If the password is really complex, a user can type only a part of it (preferably, the one that’s easy to remember), while a key will automatically ‘enter’ the remaining part.
Each service provider decides which of these standards it wants to implement and support. In case of Entra ID / Microsoft 365 accounts, MFA authentication supports the following 2 standards:
- FIDO2 – applies only to YubiKey 5 and blue Security Keys Series.
- OATH-TOTP – this method additionally requires you to install the Yubico Authenticator app.
How to set up YubiKey in Microsoft 365?
Preliminary requirements
Tenant-wide YubiKey configuration takes place in the Azure portal. To register and use keys with your Microsoft 365 tenant, you don’t need to buy a separate Entra ID license (e.g. P1 or P2). The Entra ID Free version that comes with your Microsoft 365 plan lets you use keys as the second factor of the multifactor authentication by default – similar to Microsoft Authenticator or an SMS code – but requires some additional steps on the admin’s part.
Letting your users register YubiKey devices (admin’s part)
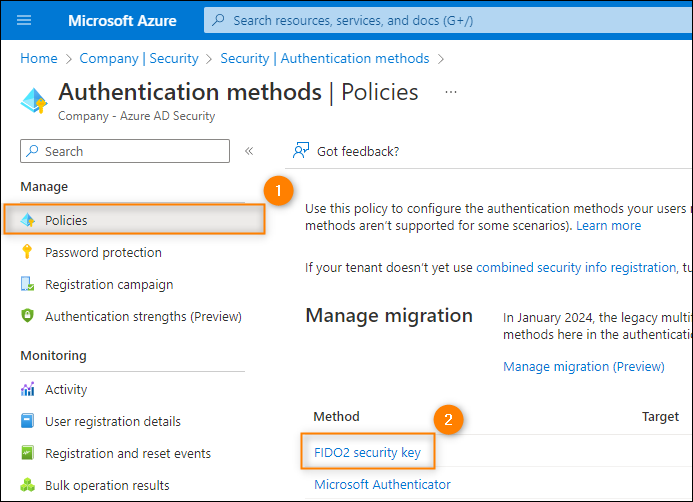
To let your users register security keys as an authentication method, you need to edit authentication policy. This is done per tenant and requires you to have the role of Security Administrator or Global Administrator. Follow the steps below:
- Sign in to Azure portal.
- In the left-hand navigation menu, go to Microsoft Entra ID > Security > Authentication methods > Policies and click FIDO2 security key.
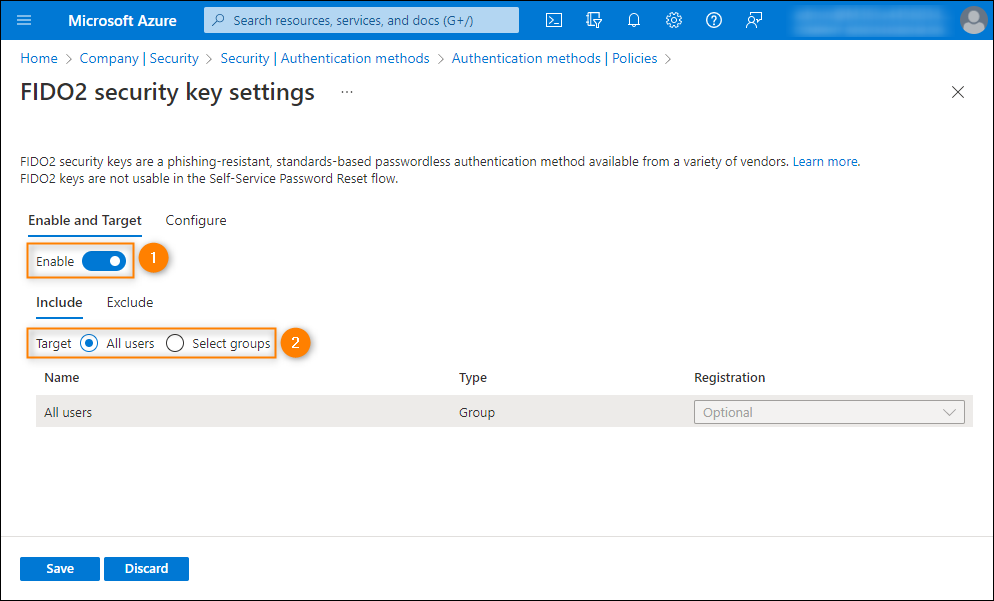
- On the Enable and Target tab, set the switch to Enable and choose the users who will be able to register and use security keys. You can select All users or add specific groups. By clicking the Exclude tab, you can choose the groups whose members won’t be able to use a YubiKey.
- The Configure tab offers more advanced options:
- Allow self-service set up – lets a user register a key through the MySecurityInfo portal by themselves. Enabling this option is required if you want to allow your users to register YubiKey devices.
- Enforce attestation – when set to Yes, lets you additionally verify a security key for metadata using the FIDO Alliance Metadata Service and additional tests by Microsoft.
- Enforce key restrictions – when set to Yes, your users will be able to register only those keys that have a specific Authenticator Attestation GUID (AAGUID). You can also block the use of keys with a specific AAGUID.
- Finally, click Save at the bottom of the window to apply your changes.
YubiKey configuration in Microsoft 365 (user’s part)
To add a security key as an authentication method for a Microsoft account, you should complete the following steps:
- Sign in at myaccount.microsoft.com.
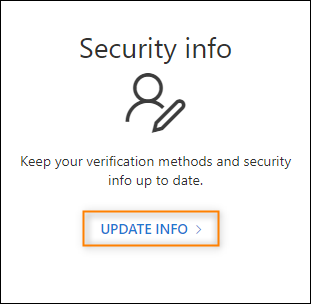
- Click UPDATE INFO on the Security info tile.
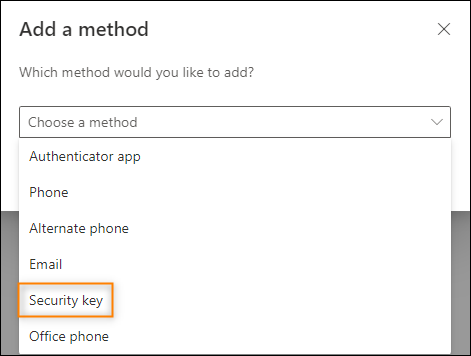
- Click Add sign-in method, choose Security key from the list, and click Add to proceed.
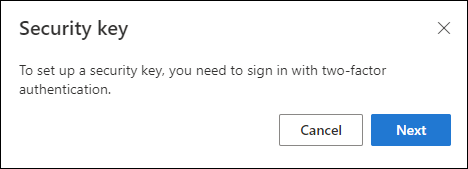
- If you already have a different MFA method configured, you will be asked to use it now (e.g. Microsoft Authenticator).
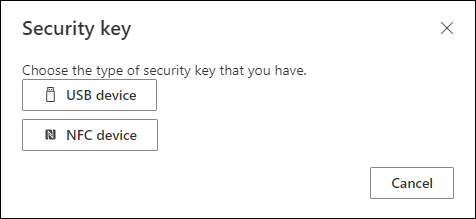
- In the next step, choose the YubiKey type you intend to use – USB device or NFC device. The configuration is identical for both types – for the sake of this tutorial, we’ll configure a USB device. Keep in mind that the NFC communication modules are currently supported by Windows-based devices only.
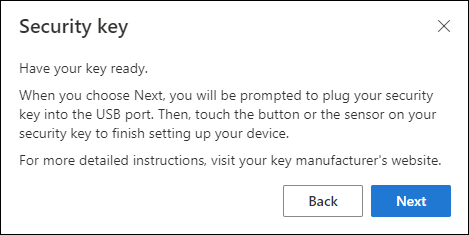
- Now, you’ll be asked to plug your key into a USB port and touch the button or sensor on it to complete the configuration. If you’re ready, plug the key and click Next.
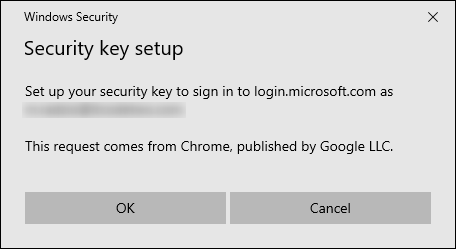
- You’ll be asked to confirm that you want to associate your YubiKey device with your Microsoft account. If all the details look fine, you can click OK. Where the request comes from depends on the browser you’re using.
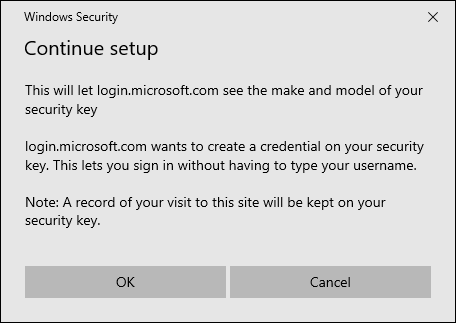
- In the next pop-up, you’ll see the information telling you what’s going to happen if you continue. Click OK to proceed.
- In the next step, you’ll be requested to create the PIN code that you’ll use to confirm any actions made with the key. The PIN must consist of 4-128 characters – a good practice is to use small and capital letters as well as digits. If you’ve already assigned the PIN to your YubiKey, simply type it in the text box.

- Now, you’ll asked twice to touch your security key – for the first time, to confirm the PIN configuration and, for the second time, to confirm the configuration of the key as the MFA method.

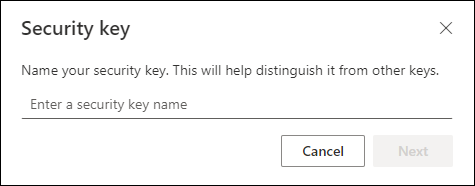
- Finally, you should give your key a name. The name will be shown on the list of the available authentication methods for your Microsoft account.
- To complete the setup, click Done – now you can use your key to sign in.
Changing the PIN / resetting to defaults
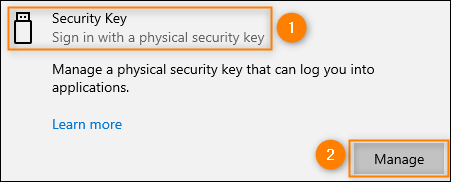
To change the PIN or reset a YubiKey device to the defaults in Windows, go to Settings > Accounts > Sign-in options, choose Security Key and click Manage.
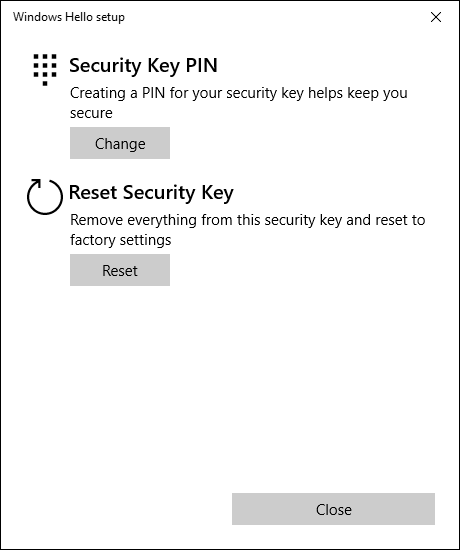
After you touch the key, you’ll see a menu where you can change your PIN (or create a new one if you haven’t done it yet) or reset the key to the factory settings. Choose the option that suits you and proceed with the instructions you see on the screen.
How to sign in to Microsoft 365 with a YubiKey device?
Passwordless sign-in
It’s the recommended sign-in method because it requires no password input.
- When you try to access a Microsoft service (e.g. Outlook on the web) and the sign in window is shown, click Sign-in options at the bottom.
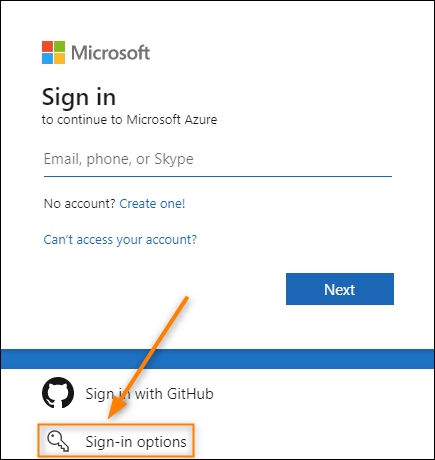
- Next, choose Sign in with a security key.

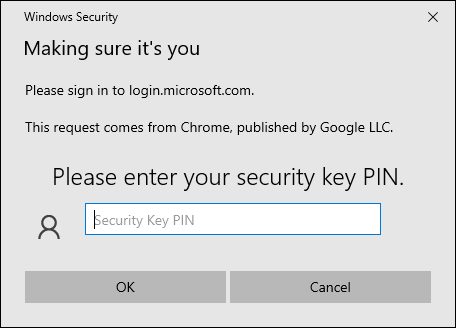
- Once you’ve plugged in your YubiKey device, you’ll be asked to enter your PIN.
- Finally, confirm your sign-in by touching the key.

- (Optional) If you have more than one Microsoft account configured, you’ll need to choose the account you want to use. After that, you’ll successfully sign in to a Microsoft 365 service.
Password + YubiKey sign-in
It’s the alternative sign-in method, but it’s less optimized (takes longer to complete) and secure (you need to enter username and password manually).
- Browse to a Microsoft service of your choice (e.g. OneDrive).
- In the sign-in window, enter your username and password.
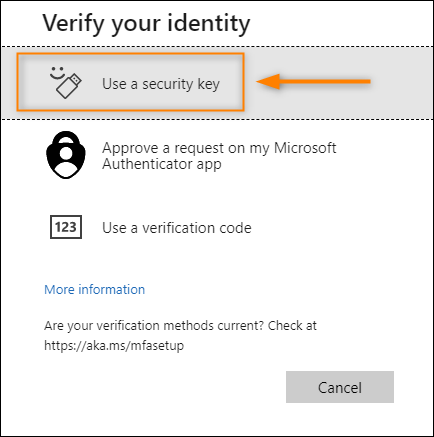
- If you have another MFA method set up, you’ll be asked to confirm that you want to sign in using the default method (e.g. the Microsoft Authenticator app). Click the option saying that you can’t use your sign-in method right now.

- Choose Use a security key from the list.
- After you’ve plugged in your YubiKey device, you’ll be asked to enter your PIN.
- Finally, confirm the sign-in by touching your security key.
Good practices
When using a YubiKey device, it’s a good idea to follow these general guidelines to enjoy better overall usefulness and security of your key:
- Have at least 2 keys at your disposal, where the second and next ones should be a 1:1 copy of the first one. If you should lose your first key or it’s stolen, you will still be able to sign in to the associated accounts and remove the stolen key. While Microsoft 365 lets you add several keys, some services don’t. Consequently, after losing a key, you need to contact a given service’s technical support.
- Keep you backup keys in a safe place that’s known only to you.
- Use a strong yet easily memorable PIN that consists of small and capital letters as well as digits. Setting your PIN to, e.g., 1234 is definitely a bad idea.
Limitations
Operating systems
Currently, iOS- and Android-based mobile devices don’t support using YubiKey as an authentication method for Microsoft 365 accounts.
In case of macOS-based devices, only Google Chrome and Microsoft Edge are supported (USB devices only). Desktop apps are not supported.
To learn which browsers in which OSes currently support using FIDO2 devices with Microsoft 365 accounts and Microsoft Entra ID (Azure Active Directory), visit this website.
Virtualization
Hyper-V
You cannot use a YubiKey device to sign in to a Microsoft 365 account from a Hyper-V hosted virtual machine (that you access via the Hyper-V or SCVMM console). The device won’t be detected by the virtual machine.
Remote Desktop Protocol (RDP)
On the other hand, a security key should work fine on machines accessed via Remote Desktop Protocol (RDP).
Azure Virtual Desktop
In case of Azure Virtual Desktop machines, you can use your key to sign in to a machine through a web browser that supports this sign-in method, e.g. by means of the Remote Desktop Web client. Learn more
What’s more, the In-session passwordless authentication feature is currently available in public preview for Azure Virtual Desktop. It allows you to ‘relay’ a security key authentication request (e.g. to enter PIN) from a virtual machine to a physical one.
The feature is enabled by default if a session host and the machine you connect from meet the following minimum OS requirements. You can also enable it manually by completing these steps:
- Sign in to the Azure portal.
- Click Virtual Machines.
- Choose Host pools from the menu and click the desired one.
- Go to RDP Properties and click Device redirection tab.
- Set the WebAuthn redirection option to WebAuthn requests in the remote session are redirected to the local computer.
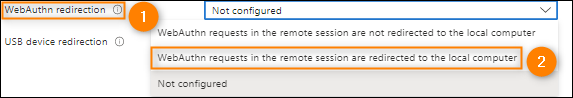
- Save your changes.
Libraries in Microsoft 365
Apps using the Azure Active Directory Authentication Library (ADAL) libraries, e.g. certain PowerShell modules like Azure AD, do not support security keys.
On the other hand, apps/modules based on the newer Microsoft Authentication Library (MSAL) libraries offer the support because they use the Web Authentication API (WebAuthn) protocol. In such a case, the communication can be handled via the web browsers that support FIDO2 devices.
Further reading


Czy za pomocą kluczy można zalogować się do kont firmowych w aplikacjach mobilnych na Androidzie i iOS np. Outlook, Onedrive?
Aktualnie aplikacje te natywnie nie wspierają kluczy sprzętowych. W przypadku iOSa, trzeba dodatkowo użyć plugina Microsoft Enterprise Single Sign On (SSO). W przypadku Androida, Microsoft pisze, że pracuje nad takim wsparciem. Więcej info na stronie Microsoftu.
I have heard a lot of things about using yubikey to log into windows without a password.
Is this possible and how do you do it?
Hi James,
Sure, you can go passwordless, as far as Windows logon is concerned.
Here’s a detailed guide where you can learn all about configuration and compatible Yubikey devices.
Cheers!