
Email traffic increases steadily each year. In 2012, users were sending 144 billion messages a day, while in 2014 this number reached 191.4 billion. According to the Radicati report, the volume of sent emails will hit the 201 billion mark in 2015. With such a big volume of data, it is quite a challenge to control mail flow effectively.
Luckily, MS Exchange Server provides various tools that help administrators tame the messaging flood. Email transport rules are one of them.
What are email transport rules in Exchange?
Exchange transport rules are very similar in operation to email rules you can find in MS Outlook. In short, they are a type of an email filter, scanning all incoming/outgoing messages, and checking if they match a previously defined condition. If the condition is matched, the rule executes a specific action on the scanned message, e.g. blocks it, forwards it, applies a prefix to its subject, etc.
Each Exchange transport rule is made up of three basic elements:
- Conditions – here you define what specific message’ properties should trigger a given action. The actions can be triggered based on: the sender’s address, email subject, message direction, and more.
- Actions – they are applied to a message, when it meets specified conditions. The list of available actions is different in every Exchange Server version.
- Exceptions – as the name suggests, here you can define what specific message attributes should stop the rule from applying an action. The list of exceptions mirrors the list of conditions.
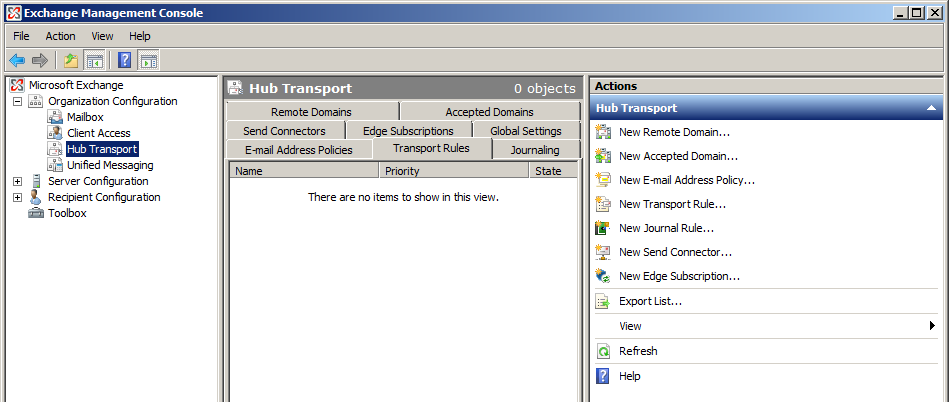
To configure a transport rule in Exchange you can use Exchange Management Console (EMC) or PowerShell. The PowerShell method is generally the same for all versions of Exchange, no matter if it is Exchange 2007, 2010 or 2013. On the other hand, the process of setting up the transport rule via EMC is different in Exchange 2013 and newer editions, as compared to earlier versions of the software.
Exchange Server 2007
To create a transport rule in MS Exchange 2007, run the EMC console first. You can find it in the Windows Start menu, in the Microsoft Exchange Server group. Once it is running, expand the following tree in its left pane:
Microsoft Exchange>Organization Configuration>Hub Transport
Click the Tranport Rules tab in the middle pane to check what rules you already have. To create a new rule launch the New Transport Rule wizard by clicking on the New Tranport Rule in the right pane. Now you can configure Conditions, Actions and Exceptions of your new rule.
Conditions and Exceptions
If the message meets a specific condition a given action is performed. On the other hand, if an exception is met – no action is applied, even if the message meets the rule’s conditions. Follow the link to see a full list of all available conditions and exceptions.
Actions
If an email matches the selected conditions then the rule can perform the following action(s):
- log an event with message – records an event to the local computer’s application log.
- prepend the subject with string – adds a string in front of the message subject.
- apply message classification – adds a special “intended use” property to the message which is then displayed in Outlook. This action helps the company to keep their communication in compliance with internal regulations.
- append disclaimer text using font, size, color, with separator, and fallback to action if unable to apply – adds a plain-text signature to the message and executes the “fallback action” when the email cannot be modified (e.g. due to the encryption). This action can handle them in three ways:
- Wrap – the original message is inserted as attachment into a new email, which is then stamped with a disclaimer.
- Ignore – delivers/sends the message without applying the disclaimer action
- Reject – the message is not delivered and its sender receives an NDR (non-delivery report).
- set the spam confidence level to value – sets the SCL value to mark possible spam messages.
- set header with value – modifies message header fields.
- remove header – removes selected message headers from the messages.
- add a recipient in the To field addresses – inserts another email address in the To field of the message.
- copy message to addresses – adds an email address of your choosing to the CC field of the message.
- blind copy (Bcc) the message to addresses – adds an email address of your choosing in the Bcc field of the message.
- redirect message to addresses – changes the To field and stops the email from being delivered to the original recipient.
- send bounce message to sender with enhanced status code – blocks the message from being delivered, deletes it and sends an NDR (non-delivery report) email to the original sender.
- silently drop the message – blocks the message and removes it without any notification to the sender/recipient.
Exchange Server 2010
Setting up a transport rule in Exchange 2010 is very similar to the method used on Exchange 2007. First, launch the Exchange Management Console from the windows Start menu. Next, in the left pane of the EMC window navigate to the following location:
Microsoft Exchange>Organization Configuration>Hub Transport
Finally create a new rule by clicking on the New Transport Rule link in the right pane. Similarly to Exchange 2007 Server, the transport rule wizard allows you to define its conditions, exceptions and actions of the rule.
Conditions and Exceptions
All conditions/exceptions from Exchange 2007 are still available in Exchange 2010, together with a number of new options. Check the Microsoft’s Technet page for a full list of transport rule predicates.
Actions
All Exchange 2007 actions are also available in Exchange 2010. In addition there are a couple of new actions as well as improvements in old ones (e.g. email signature adding) :
- add the sender’s manager as a specific recipient type – adds the email address of the sender’s manager to the To, Cc or Bcc field. The action works only if the “Manager” AD property is set.
- forward the message to addresses for moderation – this action wraps the message as an attachment and sends it in a special email to the defined user. After approving the message it is processed for delivery. If the user rejects the message, a special notification is sent to the original sender. Follow this link to learn more about moderated transport message flow.
- forward the message to the sender’s manager for moderation – similar to the above action, but instead of forwarding the message to a defined address this action forwards it to the sender’s manager.
- put message in spam quarantine mailbox – redirects the message to a special quarantine mailbox, without delivering it to the original recipient.
- rights protect message with RMS template – Data Leak Protection action. After configuring the RMS template (Rights Management Services) the transport rule can detect messages that contain sensitive data and perform a number of actions on them, e.g. block a message, restrict available sending options or limit access to an email. You can read more about RMS in Microsoft documentation.
Exchange Server 2013
This Exchange Server introduces a completely new way of controlling the mail flow via email rules. There is no MMC and all management tasks are performed within a web based console, called Exchange Admin Center (EAC).
To set up a transport rule in Exchange 2013, first launch the EAC by typing the following address in Internet Explorer directly on the server:
https://localhost/ecp
After logging in with your administrative credentials, the main EAC screen is loaded. Click mail flow in the left pane to open the screen with the rules tab. To start the rule setup, click the “+” icon on top of the list of rules. This will bring up the rule wizard.
Conditions and Exceptions
The set of available conditions and exceptions is the same as in Exchange Server 2010.
Actions
The list of available actions has been extended in Exchange 2013 and a number of new ones have been added to the wizard, that is:
- Apply a disclaimer to the message (Prepend a disclaimer) – a modification of an already available action, that adds a disclaimer at the beginning, instead of the end of the message.
- Require TLS encryption – this action requires the message to be routed outside your organization over a TLS (Transport Layer Security) encrypted connection. If there is no encryption available – the message is rejected and not delivered.
- Notify the sender with a Policy Tip – it informs senders that their messages are against the DLP (Data Leak Protection) policy configured in their organization. The action allows to notify senders and block their messages, or alternatively to notify senders and deliver their messages normally .
- Stop processing more rules – with this action selected, when a message meets the conditions configured within the rule, any subsequent rules are not processed.
- Generate incident report and send it to – allows to create a special incident report, for example, when an email that is against the DLP policy is found. The report is is then sent to a specified user. The action also optionally allows to include the original email in the report.
Exchange Server 2016/ 2019
The latest iteration of Exchange Server brings some subtle changes to email rules. Setting up a transport rule in Exchange 2016 or 2019 is the same as in Exchange 2013 (see above).
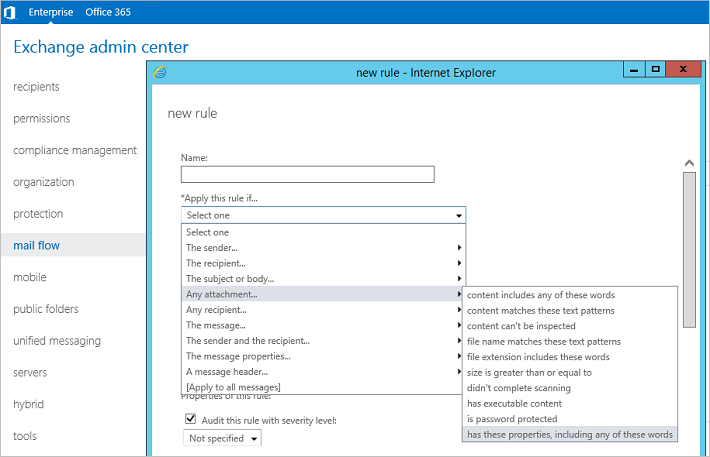
Conditions and Exceptions
In the conditions and exceptions list, there is a new option added: Any attachment has these properties, including any of these words. In other words, you select one of built-in attachment properties (e.g. Compliancy, Personal Use or Protected Heath Information) or create a custom attachment property and provide a value (specific word or words) that will trigger the action.
Actions
All actions available in Exchange 2013 are also available in Exchange 2016 and Exchange 2019. There is only one new action added.
- Notify the recipient with a message – this action sends a message (with the text you provided) to the recipient of that message. This may come in handy when e.g. some incoming emails need to be quarantined and you want to notify the recipient about it.
Summary
Whenever a new version of Exchange Server hits the market, the set of available transport rules is expanded. Unfortunately this list still lacks some important functions, for instance: placing the disclaimer right under the reply, condition based autoresponders, attachment removal from emails etc.
This is where a third party solution like CodeTwo Exchange Rules Pro may come in handy, as it provides a much richer range of email rules than Exchange:
- remove or compress attachments in messages on the fly
- redirect emails to addresses that are not in your AD
- remove sensitive information from messages (e.g. credit card numbers) before delivering them to the intended recipient
- set advanced autoreplies complete with a built in email loop protection
- add signatures and disclaimera directly under replies, instead of just at the very end of the whole email conversation
- add side banners for marketing purposes
- replace the sender’s email address
- automatically include an email unsubscribe mechanism, required legally, e.g. by CASL
- use a WYSIWYG signature template editor available with full HTML support
- benefit from a library of ready to use signature and disclaimer templates
- have the same GUI experience across all three Exchange versions
- use all available types of actions even if they are not present in a given Exchange version
- and more.
Discover the differences for yourself and see how much you can squeeze out of the transport agent capability of Exchange Server. Install CodeTwo Exchange Rules Pro in your environment and test it for free for 30 days.





Hi Adam,
is there a powershell command to run the transport rule/mail flow rule.
Hi Manju,
I’m not sure what you mean by “running” a transport rule, but there is a cmdlet to create a new transport rule: New-TransportRule. If a transport rule is in audit mode,
Set-TransportRule -Identity "YourRule" -Mode Enforcewill enable it.Hi Adam,
Where do you check to see if a transport rule has been triggered, I can’t see anything from Get-MessageTrackingLog, where I have a rule to delete an email. Auditing in the rule is enabled and according to this blog https://blogs.technet.microsoft.com/eopfieldnotes/2015/11/10/auditing-transport-rules/ should log to “message trace, extended message trace, reports”, but that’s for Exchange Online. I’m running Exchange 2010 and 2016.
Hi,
As far as I know transport rules (2010) are not able to meet my requirements forwarding NDR message in the situation (sent from outside our organization):
Internalmailbox Nr forward to external address
mbx1 [email protected]
mbx2 [email protected]
mbx3 [email protected]
Is CodeTwo able to?
Gerben
Hi,
At the moment, CodeTwo products cannot process non-delivery reports, but we will add this function to our feature requests. As for now, there is a workaround you could use to forward NDRs to external recipients, which does not require any third party tools.
Hi,
Can you share some PowerShell command using which I can generate a report for the number of emails processed or passed via a particular rule? The report should give details like email sender, recipient and subject apart from the number of emails processed via a particular rule.
Hi Vijesh,
Unfortunately, I am not aware of a way to generate such reports using PowerShell. You can use Exchange Admin Center to access detailed reports, but only in Exchange Online as for now. As long as a rule has Audit this rule with severity level checkbox selected, you can access detailed reports via Office 365 Admin Center > Reports. You can learn more about them on the following TechNet site: Monitoring, reporting, and message tracing in Exchange Online.
I have built a custom transport agent to check recipient address and if recipients email dress matches a pattern like “[email protected] get recipient name which is “sample” and call an exe to perform some actions.
The part am struggling with is I need to silently drop this email after passing it to exe how can I achieve it?
You can do this via a transport rule, run it on recipients whose email address includes mobile- and choose delete the message without notifying anyone as an action. Just make sure that your transport agent has a higher priority than the built-in Transport Rule Agent, so that the message is not deleted first. Also, be sure to test everything before implementing.
hai kamel,
i need ur assurance regarding issue
if an external organisation sending mail to my internal organisation users ,then a misspelled with one of the email address that should redirect to admin in my orgainsation how it shoould be done and which rule should be used
Hi Ravi,
You could create a mailbox which catches all emails sent to your domain, except for the ones addressed correctly. To do that, choose to apply the rule if the sender is outside the organization. Then add an exception if the recipient is a member of a distribution group containing all your users (you might need to create it yourself). Then, create a mailbox and set the mail flow rule to redirect the messages to this new mailbox. Mind that this solution might put your company at a higher risk of being attacked. Additionally, users you do not include in the distribution group I mentioned, will not get emails from external recipients. Finally, someone would need to check this mailbox to redirect emails to the right recipients.
You can consult the following TechNet article for more details: Configure a Catch-All Mailbox.
Using exchange server 2007.
Hi,
I need an exchange server rule that accepts all incoming task requests.
How can i achieve this?
Hi Kamel,
As far as I know, you can only do this via a macro. See this thread for more: http://www.experts-exchange.com/questions/21693170/Automatically-Accept-Assigned-Tasks.html
Best regards,
Adam